Disclosure: Privacy Australia is community-supported. We may earn a commission when you buy a VPN through one of our links. Learn more.
NSW Data Breach: 54,000+ Driver’s Licenses Exposed

Over 50,000 scanned NSW driver’s licences and completed Tolling Notice Statutory Declaration forms were mistakenly exposed in an online data leak.
According to reports, a cloud storage folder containing over 100,000 images was accidentally left open, exposing the driver’s licenses to the public.
As reported by Transport for New South Wales (TfNSW), Cyber Security NSW noted that the cloud storage files hosted by Amazon Web Services (AWS) containing personal information, comprising more than 50,000 photos of driver’s licences, was not properly secured.
The files also contained personal information available for public access, including birth dates, phone numbers and home addresses.
“More than 50K scanned driver licenses (front+back) and toll notices exposed in a misconfigured S3 bucket,” wrote Cyber Threat Intelligence Director and journalist Bob Diachenko in a Tweet.
“Most likely – part of NSW RMS infrastructure (Road and Maritime, New South Wales, Australia). Secured now.”
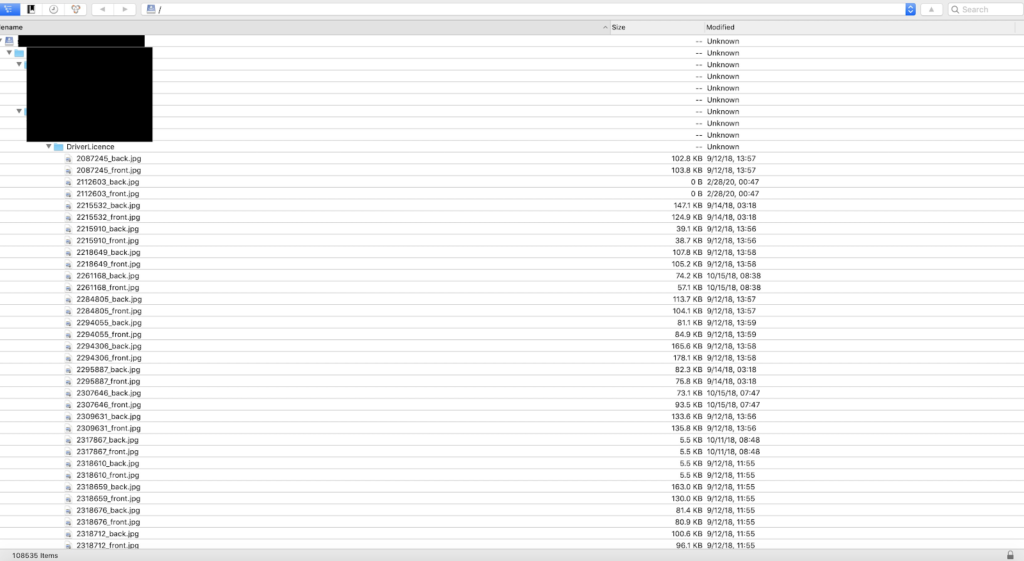
Complete Tolling Notice Statutory Declaration forms (individuals) were also found in a separate folder. When filled in by a driver, these documents contain information such as their full name, vehicle registration number, home address, phone number and date of birth.
Soon after Diachenko uncovered that scanned driver licenses and tolling notices were exposed in a misconfigured S3 bucket, he contacted Australian cybersecurity researcher Troy Hunt, who then notified the Australian Cyber Security Centre.
“All the documents I observed were related to the NSW area and there was no indication as to who might be the owner of the data,” Diachenko told ITNews in a statement.
In a statement, a spokesperson for Transport NSW mentioned that the organisation was working with Cyber Security NSW to investigate the data breach. The agency proposed that an unspecified third-party may be responsible for the breach and is denying any liability for the data leak.
“Initial information indicates the exposed AWS S3 bucket is not related to Transport for NSW or any government system,” the spokesperson said.
“While it is always important for licence holders to be privacy-aware when providing their sensitive personal information to other parties, Transport for NSW recognises that some third parties routinely request driver licence information as part of their business practices,” stated the spokesperson for TfNSW.
OAIC Statement on the NSW Data Breach
Earlier this month, the Office of the Australian Information Commissioner (OAIC) released a statement on the reported data breach involving thousands of scanned New South Wales (NSW) driver licences.
In the statement, the OAIC reported it was making inquiries with “relevant parties” into reports of the data breach involving tens of thousands of NSW driver licences.
The Australian Government agency requires organisations to act promptly in order to control data breaches involving personal data and evaluate the possible consequences of individuals affected by the breach.
Organisations covered by the Privacy Act must quickly notify anyone who has been affected by a data breach that may result in serious harm. They must also notify an eligible data breach to the Office of the Australian Information Commissioner.
To prevent data breaches from occurring, the OAIC states that organisations must be proactive in protecting personal information by implementing measures to secure personal information.
This could include improved technology and training of staff. According to the OAIC, organisations must also have a data breach response plan prepared to go in the event of a data leak.
The OAIC advises individuals to promptly respond when they are notified and to take the necessary measures, for instance, watching out for scams and checking credit reports and accounts.
As a security analyst working in Beijing in 2008, I struggled to connect to basic websites like Facebook and Wikipedia (coincidentally, many more websites are banned in China today than were then). Naturally, I started looking for a solution. VPN services were, at the time, security tools used by large IT companies or cybersecurity professionals.
I’m now the founder and CEO of Privacy Australia which I continue to run on a full-time basis and some copywriting gigs for corporate clients.
This includes finance and investment topics that have been featured on sites such as Yahoo Finance, MarketWatch, and the New York Times.
EXPERIENCE
- Senior Technology & IT Consultant
EXPERTISE
- Penetration testing
IN THE NEWS
OUR EDITORIAL PROCESS
Privacy Australia is committed to providing clear accurate, researched, and transparent information. All of our content writers and journalists follow a strict editorial process.