Disclosure: Privacy Australia is community-supported. We may earn a commission when you buy a VPN through one of our links. Learn more.
4 Best Browsers for 100% Privacy & 4 to Avoid
Did you know that every time you go online, your browser leaves a ton of information about you behind?
Anyone who gets unauthorized access to your computer will be able to review this information and learn a lot about your habits. What makes matters worse is that your browser is happy to report a lot of your private information to the websites you are visiting.
In the wake of renewed interest in privacy on the part of consumers, popular Internet browsers are always releasing blogs and sending emails proclaiming their commitment to privacy.
However, if you just scratch beneath the surface and look at their privacy statements or their terms and regulations, it becomes clear that protecting your privacy is the last thing on their mind.
For this reason, it is important for you to arm yourself with knowledge. In this guide, we will discuss how your browser may be compromising your privacy, which browsers to avoid, as well as discuss our picks for the best browsers for your desktop, Android, and IOS.
Why Most Browsers Don’t Care About Your Privacy
We place a lot of trust in our browsers. We use them look at all sorts of private, personal, and potentially embarrassing information on the Internet. We do this knowing full well that some aspects of our identity are being recorded.
Most people agree to this storing of information because they want to be able to browse the Internet easily and to keep the service free. Thankfully, some individuals have taken some steps to protect themselves by trying to find the best VPN for the browser they are using.
The problem is that most browsers might not be holding up their end of the deal. They may be selling your information to others, and that information could be used for more personalized advertising or more nefarious purposes. Just look at all of the information your browser is probably collecting about you right now.
Location
Most browsers have a built in geo location API.
The websites you visit and services you use request this information so that they can determine which version of their site they should show you.
This information can also be used in determining whether sites like BBC, iPlayer, Hulu, or Netflix should be available to you. You may be able to get around geolocation restrictions by using a VPN, even a great free VPN sometimes does the job.
The accuracy of the location information will vary depending on the device that you use. Location information is usually not as accurate as what you see on your smartphone because your smartphone uses GPS.
Connection
Some websites, like streaming services, will request information about your connection information. They can use this to determine the website content to serve you.
A streaming service like Netflix will use this to alter the stream you are viewing. You may be able to get around geo location restrictions by using a Netflix-ready VPN.
An example of such a provider is Surfshark. Surfshark has servers and systems designed specifically to get around these restrictions.
Social Media
You already know that your social media accounts are tracking you as you visit sites on the Internet. That’s why they are free. They get paid by selling you advertisers.
There is no incentive for them to stop these practices. You might think it’s no big deal that social media is tracking you, but it can cause you a lot of problems.
For example, let’s say you stay logged into Facebook and then visit a site showing nefarious items or even adult content. The social media sites remember this using what’s known as supercookies.
They’re not going to give you advertising full of adult content, but the log that your social media site made of your visit to sites with adult content will never disappear. It will always be linked to you.
Hardware
Your browser will record information about the hardware you are using and the operating systems you have installed. This is to make sure that the web information you see will actually work on your device. Your browser will also record any extensions or add-ons you have connected as well as the service provider you are using.
Gyroscope
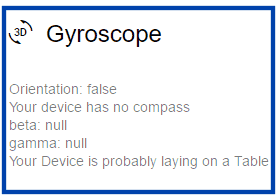
This information is only gathered on mobile devices.
What makes this information creepy is that your browser is able to use it to determine if your device is in your hands or sitting on a table.
While a lot of this information may seem innocuous, the truth is that when it is combined with the other information your browser is recording, it paints a real picture of who you are.
In the hands of less than honest people, it can be used to identify ways to attack your privacy. See for yourself what your browser knows about you.
4 Internet Browsers to Avoid
When making our pick for the Internet browsers you should avoid, we looked at a few criteria. These included the number of weeks between updates, security, and privacy.
Based on this we feel that these are Internet browsers you should not use if you wish to avoid browser hijacking and other unpleasant privacy issues.
1. Microsoft Internet Explorer

There was a time when Internet Explorer was the undisputed king in the world of browsers.
Now, Microsoft is urging people not to use Internet Explorer. That tells you just how bad it is.
Microsoft has replaced Internet Explorer with Edge. So they are planning no more major updates to IE. They still offer some security updates, but these are infrequent. Internet Explorer may go down in history as one of the least secure browsers ever created.
When it comes to privacy, Internet Explorer allows you to use pop-up blockers and to send “Do Not Track” requests not only to the sites that you have visited but also to the third-party sites that offer content on the sites you visit. Unfortunately, these requests can be ignored.
Internet Explorer is not able to guarantee that your private traffic will stay private. And Internet Explorer is closed source. So you have no idea what surveillance programs are lurking behind the curtain.
One thing I need to mention, if you’re using a good online trading platform you should under no circumstance still being using EI to trade. It’s a serious liability and you’re potentially risking leaking your financial data.
2. Microsoft Edge

Chromium-powered Edge is Microsoft’s latest attempt at creating a viable web browser. It is designed for individuals running Windows 10.
Microsoft Edge only updates twice a year.
When you think about the advanced malware and other pieces of software designed to invade your privacy that are being updated all of the time, biannual updates do not seem anywhere near enough, and it’s definitely a lot fewer than its competitors.
Edge browser runs in a sandbox. This means that the processes of the browser are contained. The idea is that the browser should be able to prevent suspicious sites with malicious code from affecting users. Edge has limited extension support.
This means there are fewer dangerous extensions you might accidentally download. However, true to form, Microsoft Edge is quickly being revealed to have a spotty security record at best.
With Internet Explorer, you have the benefit of its Tracking Protection feature. For some unexplained reason, Microsoft has decided to go without this tracking protection with Edge.
Even in private browsing mode, you can still be tracked. The conclusion is that if you are looking to browse the Internet privately, Edge is not a good option for you.
3. Opera

Opera is a Chromium-based browser that benefits from updates every four to six weeks.
The ideal scenario would be updates implemented every three or four weeks.
When it comes to safety, Opera has a number of security features that are designed to improve the safety of your browsing experience. These include fraud and malware protection and tools designed to block scripts and add-ons that make browsing insecure.
Opera does make it possible for you to customize your privacy and security settings so that your data will not be cached. However, most people are accustomed to a good browser doing this automatically, so they may not change this security setting.
What is more troubling is that Opera purchased a VPN in 2016 that has been shown to track bandwidth and log usage. If that was not disturbing enough, Opera was purchased by a company that has become infamous for privacy violations.
4. Google Chrome

Google Chrome is by far the widest used web browser today. They offer frequent updates and good security for their browser. Google has gone as far as encouraging hackers to look for vulnerabilities in its browser with the goal of finding loopholes and fixing the product.
The reason why Google Chrome is on this list and the reason why we are going to talk about it again in this guide is that Google Chrome belongs to a company that makes its living by gathering private information from the public.
Every few months it seems like Google unveils something designed to invade your privacy using Chrome, be it a questionable location history policy or automatically signing you into the browser.
Google uses Chrome to learn as much about you as they can, and then they make money from that information.
Google Chrome offers a number of browser extensions. These add functionality to your browsing experience, but they also rob you of privacy. Let’s not forget that Google Chrome is a closed source browser.
So you have no idea what they have hidden in their code. Google does offer an open source version of Chrome for those who are interested in it.
Top Four Desktop Browsers for Privacy and Safety
Anonymity on the Internet is quickly becoming a thing of the past thanks to social media networks and browsers that store your private information with the goal of providing customized advertisements and websites.
The following are browsers that we feel are the best anonymous browsers you can use for privacy and safety.
1. Tor Browser
Tor browser makes your web traffic anonymous via the Tor network (The Onion Router). As a result, it is easier to protect your identity online.
Browsing the web using Tor will be slower than using the clearnet. And there are a number of websites that block Tor users.
Authoritarian governments that are concerned about their citizens communicating, publishing, or reading information privately will also block Tor browsers.
Because of the anonymity it provides, Tor browser has become the go-to for journalists and dissidents around the world who are working in regimes that block communications.
Many view it as the bedrock of online democracy today. This is one of the reasons why researchers are diligent at improving the anonymity properties of Tor.
How Tor Browser Protects Your Anonymity
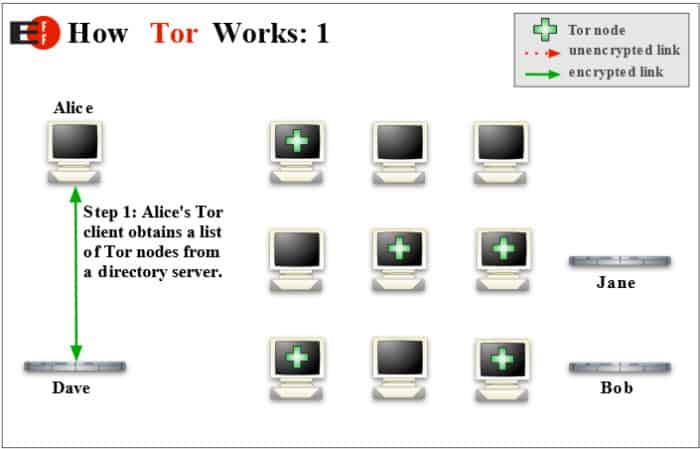
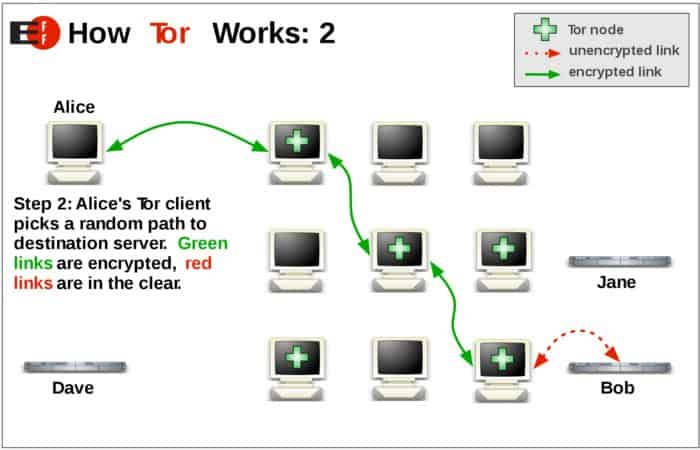
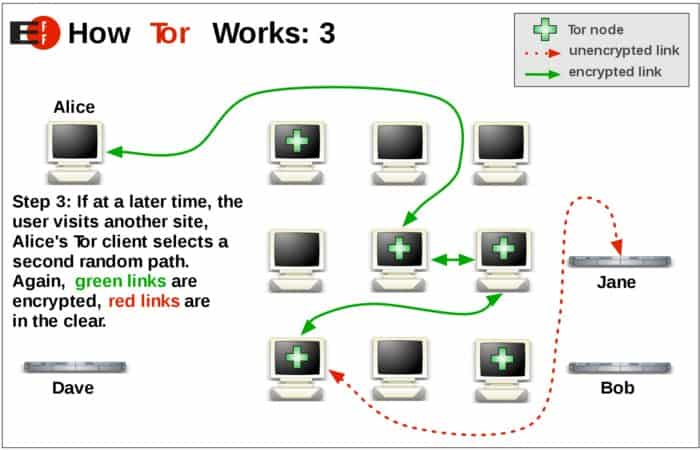
The onion icon is used to illustrate how the Tor browser works. It routes your traffic through the Tor network, making it anonymous. Tor uses a three layer proxy, similar to the layers of an onion.
Tor browser will randomly connect to a publicly listed entry node. From there, traffic is bounced through a middle relay that is selected at random. Then, traffic will exit through the final exit node.
When using Tor browser, one should not be surprised if their pages upload in another language. Google and other services use your IP address as a way of guessing the country are in and the language you will want information presented in.
However, when you use Tor, your physical location appears to be on the other side of the planet.
Individuals who live under governments that block Tor will configure their Tor browser to use bridges. Tor’s entry and exit nodes are listed publicly. IP bridge addresses are not. This makes it difficult, if not impossible, for governments to block these IP addresses.
Although Tor network can route all kinds of TCP traffic, it has been optimized for web browsing. Tor will not support UDP.
2. Epic Privacy Browser

Epic Privacy browser is an Indian-based browser that offers many of the privacy features people want straight out-of-the-box. Epic Privacy browser is built on the Chromium platform.
Some of its privacy features include:
- Not allowing plug-ins
- Blocking third-party cookies
- One click web surfing proxy
- Actively detects and blocks ad networks
- Blocks web analytics systems that track your online activity
How to Use Epic Privacy Browser
A person who is familiar with using Chrome will be able to use Epic. Download it, and start surfing. Since Epic does not to keep history, its homepage will have eight panels of your favorite sites. Two of them are populated with “How It Works” and a panel directing you to Epic’s private search.
If you want the other panels to be populated with a site when you log in, you will need to manually enter the URL you want to be there. After each browsing session, cookies, search-related data, and trackers are deleted.
How Epic Privacy Browser Protects You
One way they do this is by not sending referrer header data. This means that they do not send data about terms that you’ve searched to other websites when you click a link from a search engine.
Web RTC IP address leaking is blocked. This means that Epic automatically blocks web RTC calls that might leak your IP address. Unless you are subscribed to a VPN service that directly offers leak protection like NordVPN, these leaks can still happen with a VPN or a proxy server.
URL tracking and address bar tracking are removed. This means that the following things are removed:
- Address bar suggest
- Auto translate
- URLTracker
- URL Check
By default, Epic’s extreme privacy nature means that there is no:
- Spellcheck
- Password Saving
- Web Cache
- DNS Cache
- Auto Fill
- History
- Automated “Most Visited Websites”
When Epic closes, it will automatically delete:
- History
- Databases
- Visited Links
- Media Cache
- Log in Data
- Application and DNS Cache
- Index DB
- History provider cache
One Click Encryption Proxy
Epic’s encrypted proxy will keep your IP address hidden and encrypted as you browse. DNS requests will be routed through the encrypted proxy.
This means that your ISP, the government, your employer, and network snoops will have no idea where you are browsing from or where you are browsing to.
Learn how to protect your privacy, and stop your ISP from seeing your downloads.
3. Brave Browser
Brave browser is making a name for itself among those who are interested in privacy because it is giving users a safe, fast, and private browsing experience.
Brave prides itself on being more than a new type of browser.
Their goal is to revolutionize the way that people think about the Internet. As an open sourced browser, it has a vibrant team of individuals working on it that are privacy and performance focused. Brave was founded by the co-founder of Mozilla and the inventor of JavaScript.
What Makes Brave Run
Brave is an open-source project built on Chromium. This means that the same backend technologies used to make Chrome work, such as the V8 JavaScript engine and the Blink rendering engine, will work with Brave.
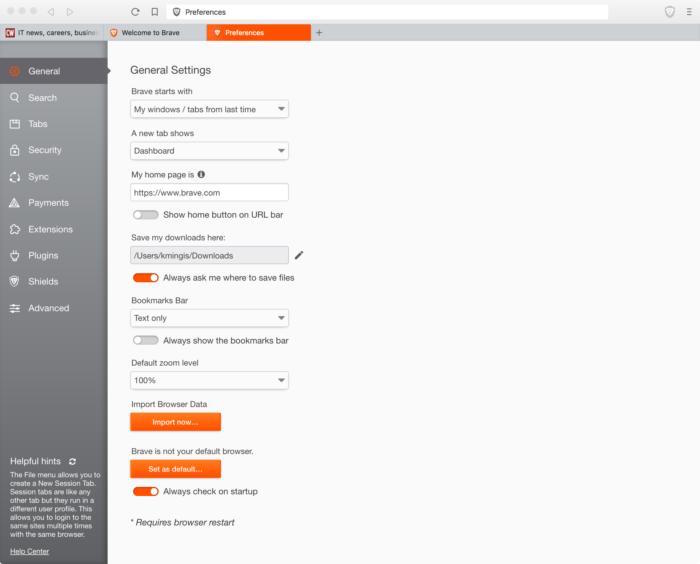
When it is run on iOS, Brave uses WebKit, the power behind Apple Safari browser.
What Makes Brave Different?
It is the attitude with which Brave aggressively opposes ads. Its business model is based on blocking ads and replacing those with ads from its network.
Brave has gotten rid of all ad trackers. However, what Brave has not removed is ads within search results. This includes AdWords advertisements within Google results. By eliminating ads, Brave is downloading a lot less content from a website that other browsers that are not using an ad blocking extension.
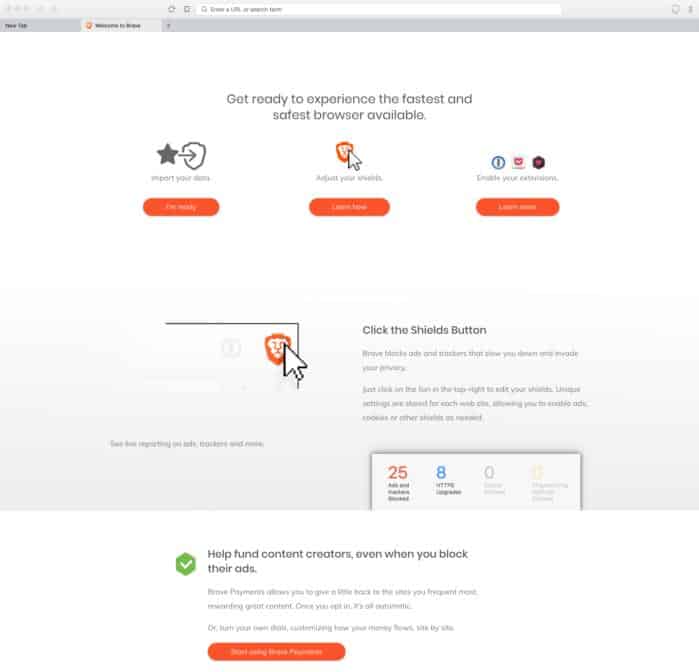
The company swears that it does not and will never store user’s data on their servers.
4. SRWare Iron Browser
SRWare Iron browser markets themselves as the browser of the future. Their focus is on maintaining privacy and security. Like many of the browsers we have reviewed, SRWare Iron implements Chromium.
It is available for free on Mac OS, Windows, and Linux. Some of the features that make it private and secure include:
- It will not track downloads or installations of the browser
- It won’t provide updates in the background, such as those seen with Google Chrome
- It offers a customizable user agent
- It will not generate a program installation ID
What Makes SRWare Iron Browser Unique?
Privacy is what sets SRWare Iron apart from mainstream browsers like Google Chrome. Here are some examples:
Suggest
Depending on how you configure Google Chrome, when you put something in the address bar, the information is sent to Google and helps them provide suggestions. This is non-existent with SRWare Iron.
Alternate Error Pages
Depending on how you configure Google Chrome, if you type in an incorrect address in the address bar, this information is sent to Google, and they send you back an error message. SRWare Iron browser does not do this.
Ad Blocker
Chrome does not come equipped with a built-in AdBlocker. SRWare Iron browser does. Their Adblocker can be easily configured by a single file.
These are just a few of the features it has. SRWare Iron browser deals with:
- User Agent
- Preview Thumbs
- Google Updater
- URL Tracker
- RL Z Tracking
- Error Reporting
Best Browser for Android
Your personal data is more valuable than gold. This makes smartphones and other mobile devices gold mines for anyone who wants your private data.
Why Firefox Focus is the Best Browser for Android Users in Search of Privacy
Mozilla’s Firefox Focus is designed for individuals who are concerned about privacy.
As soon as you close your browsing session, personal information about you, including passwords, browsing history, and cookies, are immediately deleted. Mozilla’s Firefox Focus also stops trackers and blocks ads.

How Does Firefox Focus Work to Protect Your Privacy?
Firefox Focus provides extra security by making it possible for you to block known website trackers based on categories. This means that you can select to block ad trackers, analytics trackers, or social trackers individually or as a group.
You will also be able to block things embedded in news articles, videos, and photo slideshows that might be used to track you.
In providing tracking protection, Firefox Focus makes use of a list provided by Disconnect. This list allows Firefox to identify and block trackers.
Enhanced Tracking Protection
This feature makes it possible for you to block cookies and trackers with extreme granularity. Until this feature was added, Focus would block all cookies as a default setting. You can still do that, or you can choose to allow cookies if they add to your experience as a user.
At the same time, you are preventing trackers from being able to track you over multiple sites. This means that they’re not going to be offering you the same products over and over again, nor will they be recording your online behavior.
Best iOS Privacy Browser
If you’re in the market for a private browser for your iPhone or your iPad, then just go with Ghostery Privacy browser. It will allow you to browse the Internet privately and without leaving a trace on your iOS device.
While Ghostery Privacy was acquired by Cliqz on 2017, both browsers still operate as individual entities but share security feature add-ons between each other.
Ghostery Privacy, the Fastest and Most Secure Browser for iOS
This is one of the fastest and most secure browsers for iOS. Ghostery Privacy browser provided iOS users the opportunity to browse the web quickly, privately, without trackers, and without ads.

Like all of the products Ghostery produces, their mobile browser is completely open source. At the heart of its technology are some features based on Firefox technology. Some key features of this iOS compatible browser include:
Built in AdBlocker
As a default setting, Ghostery Privacy browser gets rid of ads and clutter. Users are left with a clean and fast browsing experience. Users are shown who is tracking their data when they visit websites. They then have the option to block or to unblock trackers.
Ghost Search
This is a privacy search engine operated by its parent company, Cliqz. Cliqz is completely independent and has its own web index. Cliqz will not share personally identifiable information.
They use state-of-the-art techniques to keep the search queries of their users completely anonymous.
Ghost Mode
Users are able to protect their privacy by preventing the websites that they visit from being recorded in their browser history.
How to Optimize Chrome for Maximum Privacy (If You Have to Use It)
You may want to use some of the more secure privacy based browsers we’ve discussed in this guide. However, since Google Chrome is the most popular browser on the planet, it’s likely that you’re going to have to use it at work or in other settings.
Thankfully, there are a few adjustments you can make to the settings to improve your privacy.
1. Don’t Let Chrome Sync
If Chrome is installed on your phone, laptop, and your computer at work, it wants to sync things like your passwords and your browser history to all of the devices that it is on.
Sure, it might be convenient. But your privacy is more valuable than a little bit of convenience. You don’t necessarily want the sites you search at home or on your mobile device to be on your work computer, do you? You can fix this by doing the following:
- Click on the three dots that appear on the right-hand side of the Chrome window. This will open the menu.
- Click on settings.
- Click on “People.” You should see your Google login/account name.
- Click the sync bar just underneath your login/account name, and “Advanced Sync Settings” should appear.
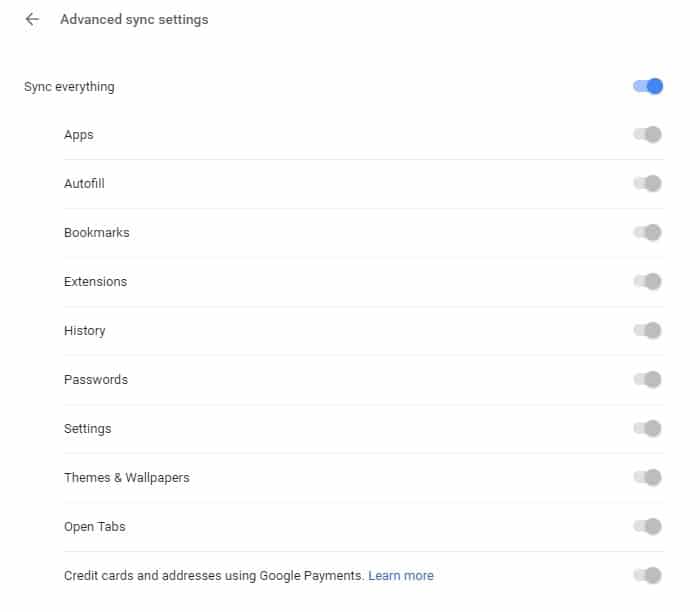
- Turn off anything you do not want the browser you are currently using to share with the browser on your other devices. You will need to make this change on each device you are logged in on.
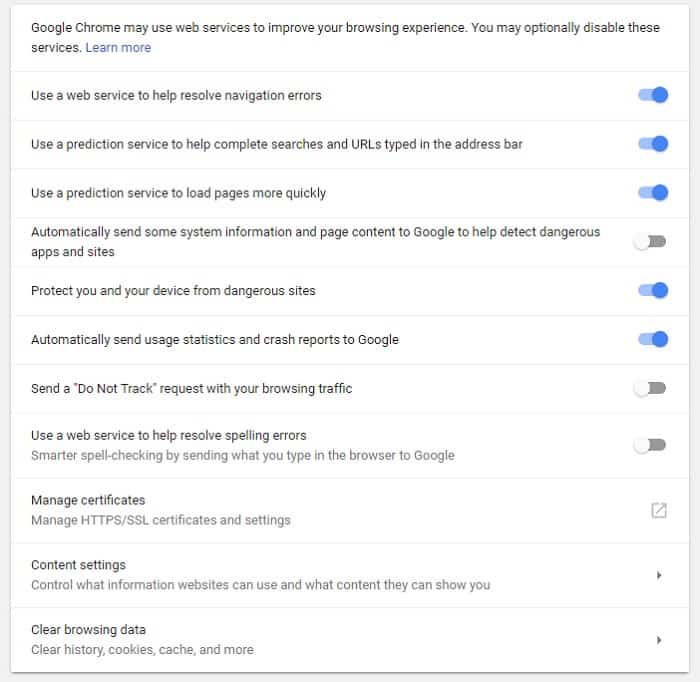
2. Control Who Chrome Chats with
Chrome interacts with a number of online services to make certain features function. If you would prefer that Chrome does not interact with these services without your knowledge, you can deactivate them one by one.
Just remember that by deactivating them, you are also going to deactivate the features they bring. To access this, do the following:
- Click on the three dots that appear on the right-hand side of the Chrome window. This will open the menu.
- Click on settings. Scroll down to the bottom of the page.
- Click the advanced arrow to gain access to privacy and security features.
- You can decide what extra settings you want to disable.
3. Control Web Content
Google Chrome allows you to control what websites may or may not do. In order to accomplish this, do the following:
- Click on the three dots that appear on the right-hand side of the Chrome window. This will open the menu.
- Click on settings. Scroll down to the bottom of the page.
- Click the advanced arrow to gain access to privacy and security features.
- Click content settings for advanced features.
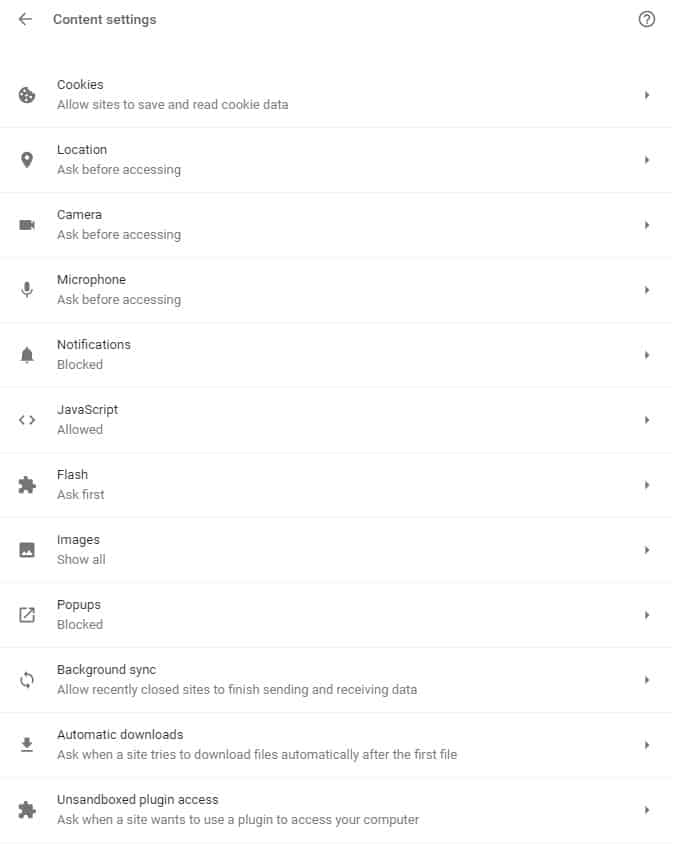
With this page open, you will be able to fine-tune your cookie settings, determine how long the data should be kept, and take steps to prevent websites from building a detailed profile about you on your computer.
Some people opt to turn JavaScript off completely and only allow it to function on websites that they truly trust.
There are other features that you may wish to switch off on Google Chrome. For example, you may want to periodically check Google Chrome’s password manager to make sure that you don’t have any stored passwords that you don’t use anymore.
If you are logged in on the browser using a shared machine, it may be a good idea to disable password management altogether.
Best Browser Plug-Ins
1. Privacy Badger

Privacy Badger is a plug-in for Google that learned to block invisible trackers.
Privacy Badger does not have a list of what it will block. Instead, it monitors the domains that seem to be tracking you as you are browsing online.
Then, it sends the Do Not Track signal. If a tracker ignores this request, Privacy Badger will start to block them. It starts the blocking process once it notices the same tracker present on three different websites.
In addition to automatic tracking, Privacy Badger prevents outgoing link click tracking on Twitter, Google, and Facebook.
2. Ghostery
Ghostery is an amazing privacy extension for Google Chrome.
It blocks unwanted ads, stops trackers, and can increase the speed with which websites load.
Ghostery lets you see who is tracking you on what website and who is collecting your data. Anti-tracking features make your data anonymous to give you an extra layer of privacy.
Conclusion
You need a well-configured and secure browser if you’re going to protect your data and keep your private information private as you are browsing the web.
Remember, most browsers are going to hold onto your private data if their default settings are not changed. This makes these browsers, and by extension you, targets for cybercriminals. Get a good VPN like NordVPN or Surfshark, and start browsing securely.
For more info about improving your online surfing experience, take a look at my recent epic review of NBN plans by area and speed.
You Might Also Like: