Disclosure: Privacy Australia is community-supported. We may earn a commission when you buy a VPN through one of our links. Learn more.
Best Crypto Software & Hardware Wallets
Storing coins correctly is still a mystery to some, despite many like Bitcoin already being mass-adopted. But to get in on the action and coins, you’ll simply need a reputable crypto wallet provider.
And holding crypto safely doesn’t need to be technical at all… Just download a ‘hot wallet,’ for max ease and speed. Or buy a ‘cold’ one, for extra security, then use a simple app.
Below, we’ve lined up the top crypto wallets perfect for all users.
Table of Contents:
- The best hot wallet
- The best cold wallets
- How to choose
- What is a private key
- How long does the average transfer take
- How do I keep my coins safe
- Should I leave my Crypto on an exchange
- What are the steps to making a Crypto wallet
- What is the best Bitcoin wallet for beginners
How We Choose our Platforms 📚
Every service on this list has a world-class reputation for security and ease of use.
To safely trade crypto in Australia, you’ll also need an encrypted wallet that is easily recoverable (which every wallet in this guide has, so that you’ll get access to your funds even if you forget your password; or if your device gets hacked, stolen, or breaks).
Best Crypto Wallets in Australia
This review article will help you choose the best crypto wallets in Australia, for you. And you can also use this as a beginner’s guide to using crypto-wallets. (Our Buying Guide and FAQ sections both can give you good awareness for the start of your journey.)
All readers are welcome to leave reviews on each wallet via the form available on each review.
‘Hot’ Wallets Section
“Hot” wallets are pieces of software created to store your cryptocurrency. Only you can access your account – which makes hot wallets the fastest, cheapest, and most convenient way to store crypto from scratch. Beginners can create and start using wallets in as little as a few minutes, without paying anything.
Interested in a Cold Storage option? Click here.
Coinbase – Most used hot wallet
Some like it hot.
Key Features:
- iOS & Android, Multiple Devices
- Very Tight Security + 2FA
- Links to Coinbase’s Exchange

Pros
- Fully regulated
- Very simple to use
- Pretty awesome fees
- Hot wallet: syncs with Coinbase
Cons
- Small number of supported coins
- Wallet “lives” online
📓 Reputation
Coinbase’s wallet is known for being one of the most trusted and secure wallets to store your cryptos.
Features
It’s very easy to use with a pretty user design that makes the wallet appealing to all levels of users; get all the following:
- Security: 2FA and multi-signature support.
- Instant access: linked directly to Coinbase’s reputable exchange.
- Diversity: Swap for or buy a diverse range of digital financial products other than just cryptocurrencies.
How to Set Up a New Coinbase Wallet:
Crypto wallets let you securely keep your coins. Coinbase’s qualifies as a “hosted” wallet, also known as a custodial or hot wallet. It’s fast to set up:
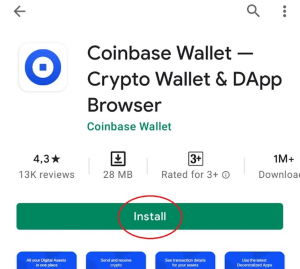
1. Install
You can install the free app for mobile (iOS and Android). Once installed, choose ‘Create a new wallet,’ accept the TOCs, and register with username and password – opt to make your wallet private or public.
Backup your wallet in the settings panel, choosing a Recovery Phrase.
2. Link with Coinbase
You’ll need an active Coinbase account, in order to do any trading (Coinbase APP). If you have this, choose ‘Connect to Coinbase’ in the settings and following instructions to link your account. Now you can send and receive crypto.
‘Cold’ Wallets Section
These are wallets that aren’t connected to the internet, other than when you are connecting them to your device. This is the safest, surest way to keep hackers out… They won’t have the chance to sniff your coins during the periods when you simply store them.
1. Ledger Nano X – Most Popular
World’s coldest.
Key Features:
- USB-C Connection
- Bluetooth-ready
- Ledger-Live Software
- Passphrase Support

Pros
- User-friendly
- High level of encryption and security
- Cold wallet: keeps offline when not in use
Cons
- Costs fair amount
- Takes time to set up
📓 Reputation
If you own many coins, want a wallet with multi-signature support, extra security, or to make regular trades with, then, the Nano X is your best friend.
This is the latest addition to Ledger’s popular range of pocket-sized HD wallets – it’s the most popular hardware crypto wallet in the world.
Features
Ledger Nano X gives you lots of cool features:
- Coin Support: Over 1000 tokens and coins, including lesser known names and meme coins. You can even store ERC-20 tokens (which are used for ICOs), though you’ll need to connect different software to your Nano wallet.
- Strong Security: The selling-point of the Nano X is cold storage for your crypto coins. Your bluetooth encryption is end-to-end encrypted (AES-based). Your private keys never leave the secure chip, with only public keys transmitted via Bluetooth.
- Intuitive design: The user interface can be accessed via smartphone and desktop. The screen is touchscreen. Ledger Live lets you set your device up, transact, and view balances whenever you want. And the actual hardware wallet is foldable and portable.
How to Set Up a Ledger Nano X Wallet:
Ledger Live gets you started in no time:
1. Set up as a new device
Tap the button next to the USB port until you see the logo. Follow the on-screen instructions, which will set up your device as new.
2. Choose PIN
You’ll see Choose PIN code showing on on-screen; each digit can be selected by the left and right buttons. Once you’ve made a 4-8 long PIN, then select the tick sign to confirm.
3. Recovery phrase
The device will then prompt you to set up a recovery phrase. Nano X will not allow you to complete the installation until you’ve created a recovery phrase, which will be automatically generated (24 words that you must store, in case of future need).
After that, install the apps on the relevant devices, which will allow you to send and receive crypto in real-time. You’re good to go.
2. Trezor One – Most Sophisticated
On the rocks. Shaken, not stirred.
Key Features:
- Open Source: Buy crypto using the Ledger app; drop straight into wallet! (Ledger Nano does not do this!)
- Features-rich
- Simple Quick Setup
- Supports Passphrases

Pros
- User-friendly
- Supports browser, iOS and Android
- Cold wallet: keeps you offline
Cons
- Costs a bit more than Nano X
- Longer setup than hosted wallets
📓 Reputation
Trezor One is a strongly established crypto hardware wallet great for beginners. It’s simple to set up and start using. It’s a super-advanced wallet that makes things simpler than Nano X. So, while it’s not quite as popular, I can’t personally see why that is the case.
Features
Trezor One gives you the following cool features:
- Coin Support: Over 1000 tokens and coins supported; purchase currencies using real cash and drop them directly into the wallet.
- Strong Security: PIN-code protected security with a high trust rating.
- Streamlined app: Lets you buy crypto using its own app and store it directly into the wallet; combining the speed of hot wallets with the ease of its simple app. You can even make your very first buys without registering; most hosted wallets don’t let you do this.
How to Set Up a Trezor One Wallet:
The Trezor One app makes buying and selling crypto as simple as making an account; you don’t even need to register to an exchange to start trading. They really combine security and speed, in this way.
Buying Guide
Let’s cover key concepts related to crypto wallets. This will give you more context before starting your new journey:
Crypto Wallets Explained 💼
A crypto wallet is really a nifty bit of SAAS (software as a service) that helps you more securely handle cryptocurrencies like Bitcoin or Ethereum.
It’s really the same thing as a physical wallet. But instead of exchanging physical notes and coins, you can hold digital coins and token cryptocurrencies (usually only a certain number.)
In fact, crypto wallets actually store your money via private keys: these are hexadecimal sequences only you and your wallet are privy to. And they need to match up with a public key, for you to actually spend its contents.
Hardware Wallets (AKA. “Cold”)

Hardware wallets can be as physical as everyday wallets in some ways. Although they look like external hard drives; they’re physical devices you can hold, and are independent of online exchanges (a storage form called cold storage).
When you purchase crypto using an online exchange, it is automatically stored online, using that exchange’s native digital storage method.
A cold storage device will ask you to connect it to your online device, to access your digital cash.
However, once your hardware wallet is given those funds, they will no longer be accessible on online servers.
This is a double-edged sword: digital cash can only be retrieved from your hardware wallet by using that device’s private key. But if you lose or break your wallet, you may well be buggered… Well, that was the case.
These days, hardware wallets have a reliable failsafe. For instance, if you were to lose your Nano Ledger device – as long as you have a backup of your recovery seed phrase, you’d only need to buy a new Ledger and that reseed would give you back access to your cash. (Just keep a good record of backups.)
Software Wallets (AKA. “Hot”) 🗂️

Software wallets are non-physical pieces of software you can download onto your device and get busy with.
A password is needed to access any coins stored. They’re encrypted. And you can recover and restore coins, as with hardware wallets, by using a recovery seed – this works even if you lose your password or your device is compromised. So it’s also the most popular way that people trade.
However, the biggest threat-point with using software wallets is their greater susceptibility to malware that may be hiding on the machine, or exposure to the internet if your device is online.
For instance, your passcode or recovery seed could be recorded onscreen by a bad actor.
Convenience is the main benefit of software wallets, on the other hand. Hacks are overall unlikely, as long as your device is adequately protected… You can use a trusted VPN to encrypt your online traffic, and up-to-date antivirus software – for better peace of mind.
Should I Buy a Software or Hardware Wallet? 🆚
I recently wrote about how $600M worth of BTC was moved by undisclosed institutions. From hot or “warm” software holdings, into cold storage. That’s a lot of money… And this is the crux with how hard and soft wallets differ. (And the key to how you choose.)
How much money do you have in crypto? The more capital at risk, the more you should consider hardware wallets; they’re simply more secure than “hot” alternatives, because they’re more difficult to hack. (And have enough backup fail-safes to protect huge sums.)
On the other hand, you’ll need to carry around a physical device for each transaction. You’ll need to pay for a device, too. So, it’s a question of utmost security vs. greater convenience: What matters most to you?
Can Crypto wallets be hacked? Techniques to look out for
Awareness is vital to good cybersecurity. In this section, I cover the most destructive and commonly-used ways hackers can jack you:
Phishing Hacks
A common trick wherein hackers steal information by making a clone website. This mirrors a legitimate platform. You are lured in via a fake email account that provides a misleading domain (such as Coinbase.co instead of Coinbase.com).
Because the UI/UX is virtually indistinguishable from the legitimate site, users are catfished into plugging in their details, which the attacker sucks up. That data is then used to access your actual account, on the real crypto website.
*To prevent phishing, avoid logging into your platform directly from an email account. And always double-check sender credentials.
Copycat Hardware Wallet
A fake hardware wallet is typically a legitimate hardware wallet that has been modified for malicious purposes. So that it is able to transmit any information inputted through it, to a secret observer.
This attack type usually targets users who have pre-existing legitimate wallets.
The victim is sent a replacement wallet with a letter warning that their current device is compromised and needs to be replaced with the newly shipped wallet. This replacement usually also includes instructions to connect it to their device and plug in their recovery key. On the instant that this is entered, it is transmitted back to the hacker.
*To avoid this kind of attack, the most important thing is awareness that this method exists.
Cryptojacking 🎃
Cryptojacking is also known as ‘malicious cryptomining’ – it’s not particularly dangerous, when compared to the other methods I’ve already covered. But it’s been popular since 2017, when the number of types of cryptocurrencies increased.

An attacker drains your idle processing power, in order to mine crypto, typically Monero, as it’s so untraceable.
Victims do not give their consent for this; their machine is ‘hijacked’ and they may be totally unaware that mining is occurring in the background. This proof-of-work goes to the benefit of the hacker.
This usually takes place through the user’s browser. No software installation is needed. Simple JavaScript (Cohive) launches this in-browser mining vehicle. On Android devices, this can lead to physical damage due to a “bloated” battery.
*Use a security tool that specifically protects against cryptojacking. Close the browser if you notice extremely high processor activity, such as loud fan activity, or dramatic CPU increases.
Malware
These vary in type and target popular OS’. A few of these viruses can target copied crypto wallet addresses (which it recognizes due to its pattern sequence). It automatically changes this to the hacker’s wallet address. (So that the victim unintentionally sends the hacker funds.)
In the past, hackers first needed to hoodwink you into downloading a piece of malicious software. Nowadays, hackers can infect your machine by redirecting you to sites with malware… Simply by accessing the site, trojans infect you and sniff out exploits, to ingest your clipboard modules.
* Once again, use a strong VPN, alongside a multi-layered antivirus. Here are a few crypto-relevant antivirus guides I’ve written:
Hacks of SMS 2FA
Two-factor authentication (2FA) by SMS is a very popular form of user verification. That said, endpoint weaknesses exist that hackers can attack through social engineering exploits.
In some instances, it’s the telecom company who is hoodwinked… The hacker intercepts an SMS verification transmission by ‘SIM swapping.’ By impersonating you, they convince telecom admins to migrate a SIM card number from your control to the attacker’s. From then on, this lets the hacker intercept 2FA messages to do with your crypto accounts.
Other more technically able interceptions exploit Signaling System 7 (SS7) endpoints. SS7 is a core feature to telecom protocols that enables the communication between differing telecom companies. It also happens to be key to the 2FA SMS feature.
* To limit the odds of this, and the possible level of devastation, use a strong password manager. This will let you avoid reusing passwords across multiple accounts. As importantly, to avoid SMS interceptions, use app-based two-factor authentications rather than via SMS.
FAQs
What is a private key?
It’s a secret number used for cryptography, which is the field of encoding and decoding data that gives you sole access to your funds.
In order to successfully transact, this private key is needed to validate, or sign, a transaction. In cryptocurrency, it proves that a blockchain (public) address actually belongs to you.
While public addresses are visible to whomever you share it with, private keys shouldn’t be shared. Private keys also protect you from theft.
If an unauthorized user tries to access your funds, they can’t do so without your private key: which is a large number-sequence that is randomly generated and contains hundreds of digits.
How much longer to receive Crypto funds?
You’ve been sent funds… Before a transaction is completed, confirmations must be carried out successfully on the blockchain.
And the number of confirmations needed depends on the transaction and cryptocurrency. (EOS is the world’s fastest.) For instance, Bitcoin requires six confirmations for each transfer.
So it depends on a few factors. Bitcoin typically can take about ten minutes and up to an hour, depending on how active the network is. BTH is relatively slow as it’s so popular.
Today, Ripple has the fastest transaction speed at around 1,500 transactions per second – which means you’ll receive your Ripple before you can count to twenty (ETH is the next-fastest).
How do I keep my Crypto safe?
A good antivirus service constantly gets updates about newly discovered threats all the time and lowers the chances of you successfully being attacked.
For mobile traders, a solid antivirus app is the first step to protecting your crypto on your phone. This is your barrier between online hazards and your personal wallet. Other than that, stick to the most well-regulated exchanges.
Should I leave my cryptocurrency on an exchange?
It’s less safe to leave significant amounts of cash on a crypto exchange… We call this using it as a ‘hot wallet,’ which is the polar opposite to cold storage.
Sure, it’s convenient to log into the same place that you buy crypto, and to see your full portfolio, patiently ready and waiting for action.
But hot wallets can be devastating when compromised… You’re a prime target for hot wallet hacks – one such notable instance being the $5.7M crypto dollars stolen from Roll’s exchange, after it was cracked open in 2021. Which is less convenient!
What are the steps to making a Crypto wallet?
Consider how you want to view funds: you may prefer your phone to a computer, or hardware wallets to simply logging on to a site. And not every wallet works across all platforms.
Before choosing, make sure your wallet supports the crypto currencies you hold, or want to invest in – being sure that they’re a well-trusted brand.
Once you’ve chosen your wallet, you’ll be given a straightforward process for setting things up, similar to creating an email account.
Either way, you’ll dramatically reduce the chances of a cyberattack if your machine and browser have sensible security measures in place. Just be sure to back up your private keys, storing them somewhere safe, in a different location.
What is the best Bitcoin wallet for beginners?
For sheer simplicity and trustworthiness, Coinbase: it’s the best-rated crypto exchange and most used crypto wallet – you can download it right onto your iOS or Android device.
With 56+ million users and a polished app that guides you through the whole process, it’s super simple to use – even for first-timers.
Coinbase’s wallet also accepts 500+ digital currencies. So, get all the other popular coins.
You Might Also Like:




